In a time where data breaches make headlines every single day, personal and entirely private and sensitive data is at risk. Of the more recent high-profile breaches, the Ashley Madison hack is arguably among the most notorious breach, if only for the kind of information revealed of consenting adults and their real identities, out in the open.
The following guide will look at practical, easy-to-use, everyday applications and habits for people who aren’t deeply technical and can still do more to better protect themselves while on the internet. The advice is given from Troy Hunt, a Microsoft Regional Director and cybersecurity expert.
First, it is important to understand and know just who you are hiding your identity from. The defense measures you apply, however simple or comprehensive they are, will depend on that singular and important question.
The privacy controls you will put to use to hide your identity from someone in the community or a shared environment, or indeed a significant other will be different to those used while staying incognito from the watchful eye of any governmental entities. While it would make sense to just get the controls for the latter, which will of course encompass privacy measures for the former, it carries with it, there could be considerable additional burden and controls to manage and implement for a comprehensive solution.
First things first, however.
Do not use your real email address. Ever.
An individual’s email address is also his or her’s easiest personal identifier, making it an easily-known and available identity attribute. A simple way to check for individuals’ presence in any website that has suffered a data breach is by combing through data breach reverse-search websites, the likes of haveibeenpwned.com or leakedsource.com.
Or, alternatively, a user can simply go to the Adult Friend Finder password reset page. Here, the reset page accepts an address, any address to then reveal if the account with the email addresses exists or not.
There’s a workaround. No, do not use your work email address either. Simply go to an email service provider, like Gmail, to make up a new email address, without using your own name.
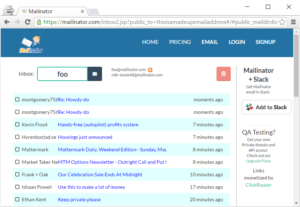
However, while Gmail and other similar service providers offer a complete email address solution, a signup process will inevitably seek a lot of information, personally identifying information. A simple alternative wherein a throwaway email can be created with minimal time and hassle is a Mailinator address. Here, you can simply create an alias for an email address like, say, jackadoo@mailinator.com before accessing all emails contained in the mailbox of the same alias.
There’s no authentication controls required and as a result, Mailinator becomes a very simple solution for those annoying setups among websites that require you to have an email to access it.
It’s important that the email address does not reveal your true identity as the email address is, singularly, the biggest identifier of an individual in the event of a data breach gone public. A simple Mailinator email address that does not seek your personal details is the go-to solution.
Create an Alias
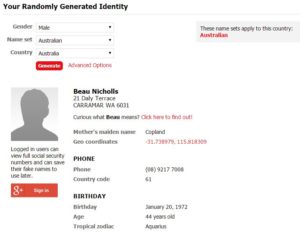
An unfortunate reality is the all-too-common practice of website seeking personal details during a sign-up. The name, date of birth, phone number, even one’s exact address is demanded, often. If there’s no legal or adverse recourse from making up those details, go head. Make them up. Once you’re done being imaginative, make sure you save those details. They are likely to come handy during identification purposes at a later time (most commonly during account unlocks, password resets etc.).
Use an encrypted keychain like a solution provided by 1Password to store those details, instead of copying them onto a notepad or text file.
You can get a fake identity generated online here.
Run into websites that seek a phone number for verification purposes? No sweat. There are free services that enable you to receive an SMS to a number that doesn’t actually belong to you, thereby safeguarding your real number from being revealed.
Alternatively, simply get a second SIM, if you have a dual SIM phone. Or get a cheap phone for that second SIM, something good enough to simply receive an SMS on.
Bottom line, your phone number is also an identifier unique to you. It’s something you do not want to be sharing.
Paying Online, Anonymously
This is a tricky one. Recovering money from a merchant can be an annoying proposition. Even more-so, if you’ve created a fake alias behind a payment that now needs to be reversed. Still, despite the cautionary disclaimer, it is possible to hide your made-up aliases when making online payments.
A good and simple way to make online purchases using a payment card is to get a virtual card, such as Entropay. It’s easy to set up, again without using your real credentials and operates like a debit card that can be topped-up from your original payment cards or bank account. Once you’ve put in money into your Entropay account, you can use the card for online purchases. Quite simply, there’s no way for the merchant to know any details of your original card.
Bitcoin is another option, but the cryptocurrency is still at its nascent stage and has a relatively small number of merchants accepting it, including the likes of Microsoft and Newegg.
Browsing Incognito. Not of the Google Chrome Variety.
When you sign up for a website, it stores some unique information, including, regrettably, your IP address. A majority of forum-type domains ascertain and store IP addresses by default, for their own moderating purposes.
Fundamentally, the information stored contain your public IP addresses, the very same address they see when you make requests to their websites. In a home network, all devices belonging in that network will have the same outbound address. Public IP addresses were discovered in the Adult Friend Finder data breach, which, needless to say, wouldn’t bode well when your significant other finds your home’s publicly facing IP among the breach.
While static IPs are steady in staying the same throughout the course of the internet connection, dynamic IPs could potentially lead to someone falsely being implicated after being tagged to an IP address that was previously used by someone else.
Google’s popular ‘Incognito mode’ has its supporters and does have its benefits. It doesn’t store your cookies, doesn’t cache any files or images and no browser history is stored. Still, it’s a completely inadequate solution when it comes to protecting your online identity, as the website still recognizes your public IP address.
A good way to use Google’s Incognito mode is to have it work alongside a VPN connection. A VPN, or virtual private network, provides an encrypted data tunnel between your computer or device and the exit node belonging to the VPN provider. Fundamentally, the website sees the IP belonging to your VPN provider, whilst yours remains hidden. This of course implies that you’re putting up a lot of trust in your VPN provider, which you can once you find the right provider for you. Typically, a good VPN provider charges for the service and while free ones exist, reliable ones are harder to find.
An alternative which is also completely free is to use the Tor network. The Tor browser bundle is readily available to download and can be used on nearly every conceivable platform including Windows, Mac and Linux.
Browsing or using the internet through Tor will see your traffic routed through multiple nodes and your IP address will be switched over and again between every jump to an exit node. There’s a downside here too, as you are trusting your web traffic to an unknown party behind an exit node, of which there are several in the Tor network.
Ultimately, no approach to online privacy and anonymity is completely foolproof. Each one has its own advantages and downsides but a good VPN, coupled with the Incognito mode will tremendously enhance your online identity protection.

