A new strain of malware that is found in the wild and is using methods of dispersal such as Dropbox and email has the means to lock Windows users out of their computers completely.
A new ransomware strain that is being distributed via email and Dropbox called “Petya” is locking users out of their computers and keeping them from regaining access to their Windows desktop unless a ransom of over $400 is paid.
The ransomware was revealed in a report by security firm Trend Micro. The link to the ransomware is included in professional correspondence emails that contains a Dropbox link.
The ransomware campaign reportedly targets employers as a message coming from professionals looking for work. Basically, the Dropbox link is purporting to help targets download resumes of those seeking employment.
As it turns out, the file is actually a self-extracting executable file that is designed to install a Trojan that blocks active security protocols in the background before downloading the Petya ransomware onto the targeted machine.
Trend Micro’s blog reads:
Not only does this malware have the ability to overwrite the affected system’s master boot record (MBR) in order to lock users out, it is also interesting to note that it is delivered to victims via a legitimate cloud storage service (in this case, via Dropbox).
Once the payload is downloaded and triggered, Petya sets out to overwrite the master boot record (MBR) of the infected OS before bringing about the dreaded blue screen of death. It gets worse, however.
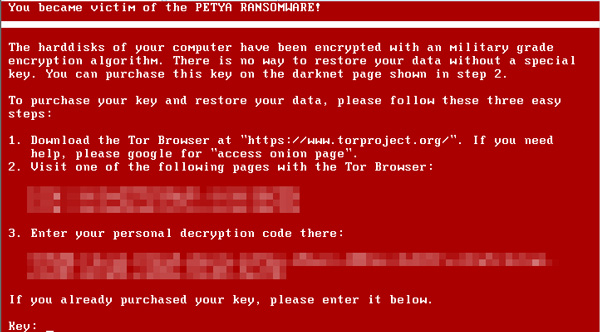
When the user tries to reboot the computer, a bright red screen pictured with an ASCII skull and crossbones turns up, a clear sign of a corrupted MBR. Noting that the ransomware has locked out the user from the operating system with a “military-grade encryption algorithm”, the victim is asked to pay 1 bitcoin, approx. $425.
The edited MBR also keeps the user from restarting into Safe Mode, which is disabled by the ransomware. Instead, a list of demands followed by a link to the Tor Project browser and the means to pay with a bitcoin is provided as instructions to the user.
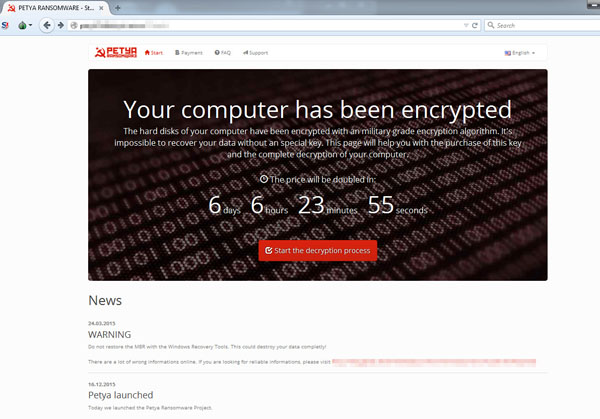
If the ransom isn’t paid within a stipulated period in time, the price would be doubled if the on-screen deadline for payment is missed.
 Images credit: Trend Micro.
Images credit: Trend Micro.

